🛡️ How to Perform a Basic Security Audit on Your IT Infrastructure
In today’s digital-first environment, your business’s IT infrastructure is the backbone of daily operations—and a prime target for cyber threats. Performing regular security audits ensures your systems are resilient, your data is protected, and your compliance obligations are met. The good news? You don’t need to be a cybersecurity expert to start.
In this guide, we’ll walk you through how to perform a basic security audit on your IT environment to identify vulnerabilities, assess risks, and take the first steps toward stronger security.
⸻
🔍 What Is a Security Audit?
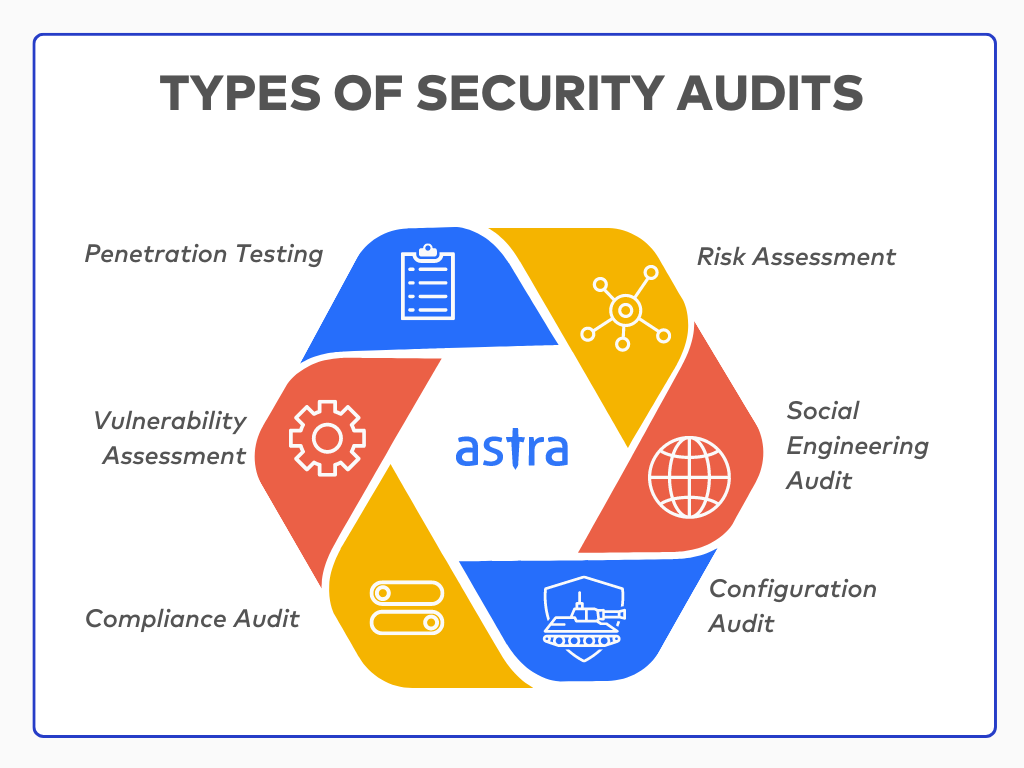
A security audit is a systematic evaluation of your company’s IT systems, policies, and procedures. Its goal is to uncover potential weaknesses and ensure your business follows best practices for data protection and system integrity.
It helps answer key questions like:
• Are we vulnerable to cyberattacks?
• Are employee devices and user accounts secure?
• Is our backup strategy working?
• Are we compliant with data privacy regulations?
⸻
🧰 Tools You’ll Need for a Basic Audit
Before jumping in, gather some key tools and access:
• ✅ A list of all devices and endpoints (computers, phones, printers)
• ✅ Your current antivirus/firewall solutions
• ✅ Access to server and network configurations
• ✅ Admin rights to your systems and cloud platforms
• ✅ An audit checklist or framework (like CIS Controls or NIST CSF)
⸻
🗂️ Step-by-Step Guide to Auditing Your IT Infrastructure
Here’s a simplified process for conducting a basic audit:
1. 🎯 Identify Your Assets
Start by cataloging your hardware, software, cloud services, and data repositories.
• Workstations and mobile devices
• Routers, servers, printers, and switches
• Installed software and applications
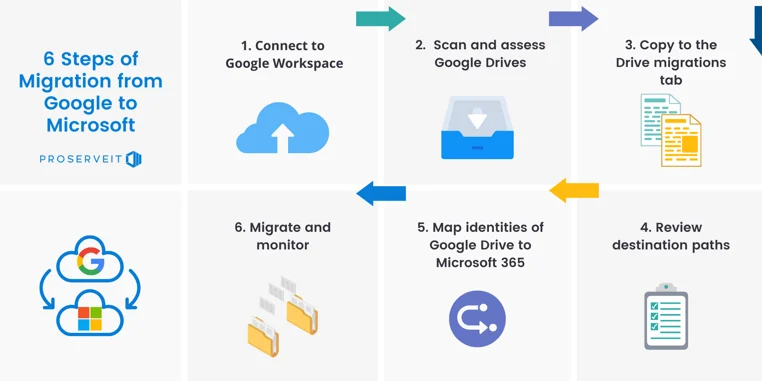
• Cloud services (e.g., Microsoft 365, AWS, Google Workspace)
• Sensitive data (customer, financial, internal)
2. 🔒 Check User Access Controls
Review who has access to what—and why.
• Do users follow the principle of least privilege?
• Are there inactive accounts that should be disabled?
• Is multi-factor authentication (MFA) enabled for all critical apps?
3. 🧱 Inspect Network Security
Analyze how well your network is protected.
• Is your firewall properly configured and up to date?
• Are Wi-Fi networks password-protected and segmented?
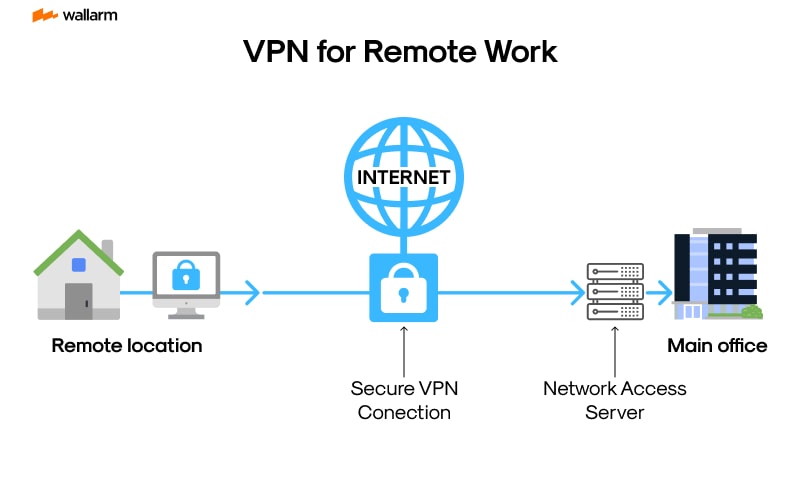
• Is remote access (VPN) secure and audited?
4. 🛠️ Examine Software and Patch Management
Outdated software is one of the biggest security risks.
• Are operating systems and apps patched regularly?
• Is automatic updating enabled?
• Are any end-of-life systems still in use?
5. 📁 Evaluate Data Backup and Recovery
Test how well you can recover from incidents like ransomware or data loss.
• Are backups performed daily (or more often)?
• Are backups stored securely offsite or in the cloud?
• Have you tested your disaster recovery process recently?
6. 📜 Review Security Policies and Training
Even the best tech won’t protect you from human error.
• Do you have up-to-date IT and security policies?
• Are employees trained on phishing, social engineering, and safe browsing?
• Is there an incident response plan in place?
⸻
🚩 Common Vulnerabilities to Watch For
While auditing, keep an eye out for:
• Weak or reused passwords
• Lack of endpoint protection on devices
• Open network ports or unsecured Wi-Fi
• Employees using personal devices without security protocols
• No data encryption for sensitive files
⸻
🧭 Next Steps After Your Audit
Once you’ve completed the audit, here’s what to do:
1. ✅ Document all findings clearly.
2. 🛠️ Prioritize and remediate critical vulnerabilities first.
3. 🔁 Schedule regular follow-up audits (quarterly or semi-annually).
4. 📈 Consider professional vulnerability scanning and penetration testing.
⸻
📞 Need Help Securing Your Business?
Conducting a security audit is just the beginning. At VertexPro.io, we help businesses like yours identify vulnerabilities, implement robust security frameworks, and stay protected year-round.
Want a deeper audit or a custom security strategy? Contact us today to speak with our experts and take the first step toward a more secure future.